
Not long ago, a maxim held that it wasn’t a question of if, but when, a crisis will strike. That’s still true. But now we should rephrase it to ‘It’s not if, but when, a crisis or cyberattack will strike.’
And when cybercrime hits, you realize quickly it’s very different from almost any other crisis. It requires a tailored and measured approach to communicating with stakeholders.
In the event of a cyberattack:
- Are you ready to comply with regulatory requirements? Do you need to be? Will others handle it?
- Since many cyberattacks disable platforms and systems, do you have back-up channels so you can communicate with stakeholders?
- Do you have a back-up list of employee and stakeholder contacts?
- Are you ready to respond publicly without inciting threat actors to wreak more havoc on the brand?
These are just a few of the questions communicators must answer without hesitation when there’s a cybercrime.
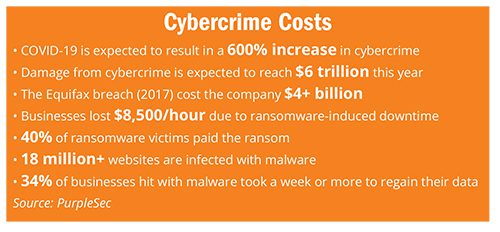
Moreover, the stakes couldn’t be higher (see chart). PurpleSec says U.S. companies lose an average of $4.13 million per cyberattack.
So, to ensure you’re not caught flat-footed, here are preparation tips.
Know Regulation/Reporting
In some companies, legal and regulatory departments handle reporting. On the other hand, let’s assume you, the communicator, is responsible for it.
So, you’ll need a working knowledge of compliance and reporting requirements. That will entail monitoring regulatory issues and double-checking your knowledge periodically with lawyers.
Irrespective of the industry and whether your company is public or private, there’s a lot to know.
For instance, publicly traded companies must file a U.S. Securities Exchange Commission Form 8-K to “announce major events that shareholders should know about.” Failure to do so can result in fines and other punitive measures.
Other examples: For financial institutions (FI), if customer data is misused or breached, the FI must inform regulators in a specified timeframe, per the Gramm-Leach-Bliley Act.
Similar regulations apply at the state level. For example, when a cyberattack hits a NY-based FI, it must follow compliance protocols outlined in the New York Department of Financial Services Cybersecurity Regulation.
And last, if a cyberattack occurs at a healthcare system or hospital in which patient data is compromised, the Federal Trade Commission has regulation concerning patient notification.
Join the Cyber Response Team
A senior communicator should be part of, not adjacent to, the company’s Cyber Incident Response Team.
Building a bridge between IT, legal, the C-suite and outside partners will ensure communicators have timely access to cyberattack information.
Access is half the battle. It will help quicken review and approval of content you’ll communicate as events unfold.
Gauge Transparency
The last thing you want is for communication to further incite threat actors.
If your company is in the middle of a cyberattack–especially one that involves ransom negotiations and stolen data–communication must strike a balance.
How or when you communicate can influence ransom demands, the length and severity of an attack and release of stolen information.
Your job is to address stakeholders’ key concerns without offering information that might further compromise network security.
Thinking like a threat actor and knowing what will and won’t incite them is paramount.
Build Back-up Systems
Let’s say your company primarily uses email to communicate with employees and other stakeholders. Yet email is down because of a cyberattack.
At this critical moment, communication must continue uninterrupted.
So, make certain there are back-up communication channels. And that you have access to platforms with contact information for stakeholders.
As these must be mobilized quickly and effectively, holding periodic drills with staff is recommended.
Companies should consider cloud-based platforms that foster one- and two-way communication that can go live at a moment’s notice.
[Dark sites is another option. See page 6.]
Be Fast But Accurate
Speed is important, but accuracy matters more. During a cyberattack, a slow, ineffective response could prove disastrous for a company’s reputation.
Still, inaccurate and incomplete information quickly delivered will cause even more damage.
When a crisis communication infrastructure is combined with legal, compliance, operations and IT entities, the chances of communicating accurately and swiftly are far better.
Ted Birkhahn is president of HPL Cyber
