On the morning of June 6, 2012, reports began circulating that about 6 million passwords attached to professional social network LinkedIn’s accounts had been compromised. The same day, in response, LinkedIn issued a press release generally acknowledging the breach while vowing to invalidate passwords of the affected accounts, and promising to send a series of e-mails to members with affected accounts.
LinkedIn’s initial actions on that day couldn’t prevent a groundswell of criticism that has dogged the company since, centering on the handling of the crisis and how a hack by an overseas forum could occur inside a top technology company in Silicon Valley.
As a longtime LinkedIn user and a monthly paid subscriber to its professional offering, Jason Maloni, senior VP at Levick Strategic Communications, was disappointed by LinkedIn’s response to its members. “They should have had a little button or alert on my homepage that stated ‘click for more information’ for my benefit,” says Maloni. A public announcement was an appropriate response, but Maloni says an organization needs to communicate a security breach through as many stakeholder channels as possible, particularly on the main destination of its users. Make no mistake: Maloni likes LinkedIn, but that’s why he expected more from them in response to the breach.
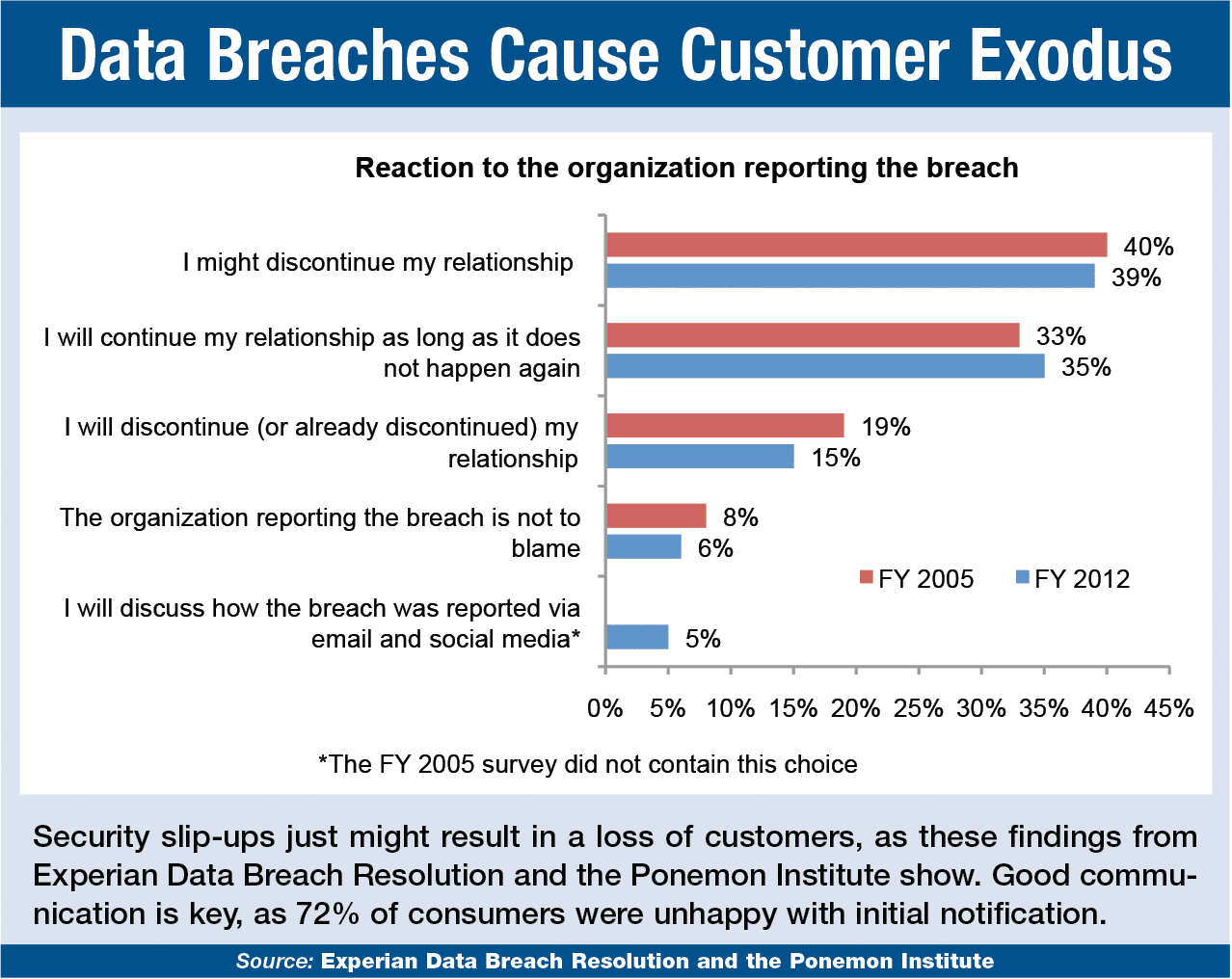 |
Maloni, who has handled several security crises for Levick clients, is not alone in his expectations. According to a study released in June 2012 by Experian Data Breach Resolution and the Ponemon Institute, 72% of 700 consumer respondents who received notification of a data breach were dissatisfied with the communication, and often wanted more information. Consequently, nearly 40% said they might discontinue their relationship with the organization (see chart).
PR’S PURVIEW
Offering complete details around a breach is a PR/communications responsibility, says Pete Pedersen, EVP and global chair of Edelman’s technology practice. Historically, data security issues have been relegated to IT and/or the legal department of an organization, leaving PR out of the loop.
It’s a different ballgame today, says Pedersen, given the 24/7 news cycle and the rise of social media. “It’s become a reputational issue,” he says. “That’s why the No. 1 priority for communicators should be to make sure they have a robust privacy policy in place for customers and other stakeholders.”
The privacy policy (see sidebar) is just one preventative measure communicators should take before a security breach occurs. Here’s the full rundown from Pedersen.
1. Deploy proactive and transparent communication of what the privacy policy is: “They are often riddled with legalese and language that is tough to understand,” says Pedersen.
2. Engage with industry advocacy groups and stakeholders: Put your policy in front of them for feedback. “That can really help in terms of trust and reputation if a breach does occur,” says Pedersen.
3. Communicate the risks of a security breach to other departments: “We’re operating in an environment of heightened sensitivity,” says Pedersen. Thus, every part of an organization should know about the threat.
SECURITY CRISIS PLAN
Setting policy and ensuring everyone is aware of the risks are just two steps. A comprehensive communications plan is also a requirement. In formulating and executing such a plan, Levick’s strategy is to divide key players into what Maloni describes as a “big three-headed dog”: legal, communications and forensics (IT).
Regularly run this dog through its paces with security-specific exercises, says Maloni, who points out that no organization is too small (or too big) to devote time to prepare itself from a security breach.
Last month, Levick worked with a university after an employee had their laptop stolen from their car. “This was not the classic hacker story,” says Maloni, but the communications are much the same.
As for LinkedIn, PR News invited the company to talk about the PR around their crisis, but a spokesperson said they were too busy dealing with the fallout—proving that even an established tech company can get into prolonged trouble from a data security crisis. PRN
CONTACT:
Jason Maloni, [email protected]; Pete Pedersen, [email protected]; Robert Connelly Jr.; [email protected].
Follow Scott Van Camp: @svancamp01
